MALWAREBYTES LOG
Malwarebytes' Anti-Malware 1.31
Database version: 1456
Windows 5.1.2600 Service Pack 2
12/5/2008 10:51:45 PM
mbam-log-2008-12-05 (22-51-45).txt
Scan type: Full Scan (C:\|)
Objects scanned: 239263
Time elapsed: 2 hour(s), 1 minute(s), 9 second(s)
Memory Processes Infected: 3
Memory Modules Infected: 3
Registry Keys Infected: 23
Registry Values Infected: 4
Registry Data Items Infected: 0
Folders Infected: 8
Files Infected: 104
Memory Processes Infected:
C:\Documents and Settings\All Users\Application Data\dqzezixw\pkpypkxq.exe (Trojan.Downloader) -> Unloaded process successfully.
C:\Documents and Settings\All Users\Application Data\dqzezixw\pkpypkxq.exe (Trojan.Downloader) -> Unloaded process successfully.
C:\Program Files\XP_Antispyware\XP_Antispyware.exe (Rogue.XPAntiSpyware) -> Unloaded process successfully.
Memory Modules Infected:
C:\Program Files\XP_Antispyware\htmlayout.dll (Rogue.AntivirusPro2009) -> Delete on reboot.
C:\Program Files\XP_Antispyware\AVEngn.dll (Rogue.XPAntiSpyware) -> Delete on reboot.
C:\Program Files\XP_Antispyware\pthreadVC2.dll (Rogue.XPAntiSpyware) -> Delete on reboot.
Registry Keys Infected:
HKEY_CLASSES_ROOT\CLSID\{2E5A65BB-B055-C0DD-0118-09975F2EE086} (Trojan.FakeAlert.H) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\minibugtransporter.minibugtransporterx (Adware.Minibug) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\minibugtransporter.minibugtransporterx.1 (Adware.Minibug) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{04a38f6b-006f-4247-ba4c-02a139d5531c} (Adware.Minibug) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{2b96d5cc-c5b5-49a5-a69d-cc0a30f9028c} (Adware.Minibug) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{0656a137-b161-cadd-9777-e37a75727e78} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{0b682cc1-fb40-4006-a5dd-99edd3c9095d} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{0e1230f8-ea50-42a9-983c-d22abc2eeb4c} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{9dd4258a-7138-49c4-8d34-587879a5c7a4} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{b8c0220d-763d-49a4-95f4-61dfdec66ee6} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{c3bcc488-1ae7-11d4-ab82-0010a4ec2338} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{000000da-0786-4633-87c6-1aa7a4429ef1} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{54645654-2225-4455-44a1-9f4543d34545} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{5c7f15e1-f31a-44fd-aa1a-2ec63aaffd3a} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{4d25f926-b9fe-4682-bf72-8ab8210d6d75} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Typelib\{3c2d2a1e-031f-4397-9614-87c932a848e0} (Adware.Minibug) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{5929cd6e-2062-44a4-b2c5-2c7e78fbab38} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{00a6faf1-072e-44cf-8957-5838f569a31d} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{53e0b6e8-a51d-448b-b692-40b67b285543} (Adware.180Solutions) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\xp_antispyware (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\XP_Antispyware (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify\__c0047209 (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Multimedia\WMPlayer\Schemes\f3pss (Adware.MyWebSearch) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad\straplcmd (Trojan.FakeAlert.H) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run\za6bww5oag (Trojan.FakeAlert.H) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\URLSearchHooks\{4d25f926-b9fe-4682-bf72-8ab8210d6d75} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\xp antispyware 2009 (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
C:\WINDOWS\mslagent (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\Program Files\akl (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\Inet Delivery (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\smp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware (Rogue.XPAntiSpyware) -> Delete on reboot.
C:\Program Files\XP_AntiSpyware\data (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\Microsoft.VC80.CRT (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Start Menu\Programs\XP_Antispyware (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
Files Infected:
C:\Program Files\uqbjlwd\StrAplCmd.dll (Trojan.FakeAlert.H) -> Delete on reboot.
C:\Documents and Settings\All Users\Application Data\dqzezixw\pkpypkxq.exe (Trojan.FakeAlert.H) -> Quarantined and deleted successfully.
C:\Program Files\XP_Antispyware\htmlayout.dll (Rogue.AntivirusPro2009) -> Delete on reboot.
C:\Program Files\MSN Messenger\riched20.dll (Adware.MyWeb.FunWeb) -> Quarantined and deleted successfully.
C:\WINDOWS\karna.dat (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\karna.dat (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\2_mslagent.dll (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\mslagent.exe (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\uninstall.exe (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\Program Files\akl\akl.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\akl\akl.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\akl\uninstall.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\akl\unsetup.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\Inet Delivery\inetdl.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\Inet Delivery\intdel.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\smp\msrc.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\AVEngn.dll (Rogue.XPAntiSpyware) -> Delete on reboot.
C:\Program Files\XP_AntiSpyware\pthreadVC2.dll (Rogue.XPAntiSpyware) -> Delete on reboot.
C:\Program Files\XP_AntiSpyware\Uninstall.exe (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\wscui.cpl (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\XP_Antispyware.cfg (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\XP_AntiSpyware.exe (Rogue.XPAntiSpyware) -> Delete on reboot.
C:\Program Files\XP_AntiSpyware\data\daily.cvd (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\Microsoft.VC80.CRT\Microsoft.VC80.CRT.manifest (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\Microsoft.VC80.CRT\msvcm80.dll (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\Microsoft.VC80.CRT\msvcp80.dll (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Program Files\XP_AntiSpyware\Microsoft.VC80.CRT\msvcr80.dll (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Start Menu\Programs\XP_Antispyware\Uninstall.lnk (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Start Menu\Programs\XP_Antispyware\XP_Antispyware.lnk (Rogue.XPAntiSpyware) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\mcrh.tmp (Malware.Trace) -> Quarantined and deleted successfully.
C:\WINDOWS\a.bat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\base64.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\FVProtect.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\userconfig9x.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\winsystem.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip1.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip2.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip3.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zipped.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\bdn.com (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\iTunesMusic.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\mssecu.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\akttzn.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\anticipator.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\awtoolb.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\bdn.com (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\bsva-egihsg52.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\dpcproxy.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\emesx.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\h@tkeysh@@k.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\hoproxy.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\hxiwlgpm.dat (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\hxiwlgpm.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\medup012.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\medup020.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\msgp.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\msnbho.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\mssecu.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\msvchost.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\mtr2.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\mwin32.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\netode.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\newsd32.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\ps1.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\psof1.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\psoft1.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\regc64.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\regm64.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\Rundl1.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\sncntr.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\ssurf022.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\ssvchost.com (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\ssvchost.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\sysreq.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\taack.dat (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\taack.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\temp#01.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\thun.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\thun32.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\VBIEWER.OCX (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\vcatchpi.dll (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\winlogonpc.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\winsystem.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\WINWGPX.EXE (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\drivers\beep.sys (Fake.Beep.Sys) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\dllcache\beep.sys (Fake.Beep.Sys) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\~.exe (Trojan.Downloader) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\vbsys2.dll (Trojan.Clicker) -> Quarantined and deleted successfully.
C:\WINDOWS\brastk.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\_scui.cpl (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\brastk.exe (Trojan.FakeAlert) -> Delete on reboot.
C:\WINDOWS\system32\wini104552502.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\tmlpcert2007 (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\swiynfj_navps.dat (Adware.NaviPromo) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\swiynfj_nav.dat (Adware.NaviPromo) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\delself.bat (Malware.Trace) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn2 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn3 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn4 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn5 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn6 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn7 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn8 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Documents and Settings\Sloane\Local Settings\Temp\wrdwn9 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
************************
COMBOLOG
ComboFix 08-12-05.02 - Charles 2008-12-05 23:06:14.1 - NTFSx86
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.673 [GMT -5:00]
Running from: c:\documents and settings\Charles\Desktop\ComboFix2.exe
* Created a new restore point
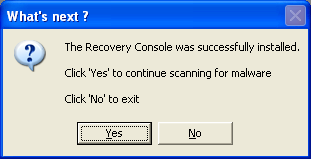
WARNING -THIS MACHINE DOES NOT HAVE THE RECOVERY CONSOLE INSTALLED !!.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin1.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin10.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin11.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin12.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin13.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin14.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin15.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin2.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin3.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin4.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin5.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin6.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin7.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin8.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMin9.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod1.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod2.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod3.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod4.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod5.zip
c:\documents and settings\All Users\Application Data\Spybot - Search & Destroy\Recovery\CnsMinZsMod6.zip
c:\documents and settings\Sloane\Cookies\akewanany.com
c:\documents and settings\Sloane\Cookies\cutib.com
c:\documents and settings\Sloane\Cookies\deqymis._dl
c:\documents and settings\Sloane\Cookies\fatirojij.bin
c:\documents and settings\Sloane\Cookies\tedoteg._sy
c:\documents and settings\Sloane\Cookies\xojemo.db
c:\documents and settings\Sloane\Cookies\xumepe.db
c:\documents and settings\Sloane\Cookies\zyqyt.db
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\cijyhehax.dat
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\ipotyved._dl
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\jadyl.sys
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\purevejaty._dl
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\ugenybi.scr
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\usamemoge.bin
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\vafan._dl
c:\documents and settings\Sloane\Local Settings\Temporary Internet Files\wepurom.com
c:\documents and settings\Sydney\Cookies\unebygewu.dat
c:\documents and settings\Sydney\Local Settings\Temporary Internet Files\fego.reg
c:\documents and settings\Sydney\Local Settings\Temporary Internet Files\ubivanely.vbs
c:\program files\livestream
c:\program files\livestream\img\p2e_1_3.bmp
c:\program files\livestream\img\p2e_2_3.bmp
c:\program files\livestream\img\p2e_3_3.bmp
c:\program files\livestream\img\p2e_go_3.bmp
c:\program files\livestream\img\p2e_logo_2.bmp
c:\program files\livestream\p2e\p2e_1.206.1.htm
c:\program files\livestream\p2e\p2eredir.htm
c:\windows\Downloaded Program Files.\cnsdtu.cab
c:\windows\Downloaded Program Files.\CnsDtu.dll
c:\windows\Downloaded Program Files\sms.ico
c:\windows\Downloaded Program Files\taobao.ico
c:\windows\Downloaded Program Files\yahoomsg.ico
c:\windows\Downloaded Program Files\ymail.ico
C:\xcrashdump.dat
.
((((((((((((((((((((((((( Files Created from 2008-11-06 to 2008-12-06 )))))))))))))))))))))))))))))))
.
2008-12-05 20:41 . 2008-12-05 20:41 <DIR> d-------- c:\program files\Malwarebytes' Anti-Malware
2008-12-05 20:41 . 2008-12-05 20:41 <DIR> d-------- c:\documents and settings\Charles\Application Data\Malwarebytes
2008-12-05 20:41 . 2008-12-05 20:41 <DIR> d-------- c:\documents and settings\All Users\Application Data\Malwarebytes
2008-12-05 20:41 . 2008-12-03 19:52 38,496 --a------ c:\windows\system32\drivers\mbamswissarmy.sys
2008-12-05 20:41 . 2008-12-03 19:52 15,504 --a------ c:\windows\system32\drivers\mbam.sys
2008-11-27 11:26 . 2008-11-27 11:26 <DIR> d-------- c:\program files\Trend Micro
2008-11-11 18:37 . 2008-11-11 18:37 13,270 --a------ c:\program files\Common Files\gipelyq.dat
2008-11-07 05:54 . 2008-11-07 05:54 11,189 --a------ c:\windows\suzohyc.reg
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-12-06 03:55 --------- d-----w c:\program files\uqbjlwd
2008-12-06 03:51 --------- d-----w c:\program files\MSN Messenger
2008-12-06 03:51 --------- d-----w c:\documents and settings\All Users\Application Data\dqzezixw
2008-11-30 05:22 --------- d-----w c:\documents and settings\Sloane\Application Data\LimeWire
2008-11-02 23:16 19,276 ----a-w c:\windows\tydyrex.scr
2008-11-02 23:16 18,457 ----a-w c:\program files\Common Files\ipiseh._sy
2008-11-02 23:16 13,799 ----a-w c:\windows\asuviwaky.bat
2008-11-02 23:16 13,625 ----a-w c:\program files\Common Files\qivi.lib
2008-11-02 23:16 12,716 ----a-w c:\documents and settings\Sloane\Application Data\ujowo.pif
2008-11-02 23:16 11,939 ----a-w c:\documents and settings\Sloane\Application Data\sito.scr
2008-11-02 23:16 11,835 ----a-w c:\documents and settings\Sloane\Application Data\ifydihy.dll
2008-11-02 23:16 10,833 ----a-w c:\windows\vuqogeg.reg
2008-10-31 04:31 19,804 ----a-w c:\documents and settings\Sloane\Application Data\uxaholicaz.scr
2008-10-31 04:31 18,272 ----a-w c:\documents and settings\All Users\Application Data\tufumicyro.scr
2008-10-31 04:31 17,162 ----a-w c:\documents and settings\Sloane\Application Data\edikuryko.sys
2008-10-31 04:31 16,938 ----a-w c:\windows\zebumu.bin
2008-10-31 04:31 15,127 ----a-w c:\windows\ruquqogavi.reg
2008-10-31 04:31 13,803 ----a-w c:\documents and settings\All Users\Application Data\zaryquzaw.com
2008-10-31 04:31 12,495 ----a-w c:\documents and settings\All Users\Application Data\wukedy.pif
2008-10-31 04:31 11,053 ----a-w c:\program files\Common Files\gaveju.reg
2008-10-31 04:31 10,507 ----a-w c:\windows\zilucoka.exe
2008-10-31 00:30 15,021 ----a-w c:\program files\Common Files\hije.dat
2008-10-29 22:03 17,338 ----a-w c:\program files\Common Files\lyza.ban
2008-10-29 22:03 16,749 ----a-w c:\documents and settings\Sydney\Application Data\boca.dll
2008-10-29 22:03 16,358 ----a-w c:\windows\tadame.exe
2008-10-29 22:03 14,939 ----a-w c:\windows\wixodocyw.bat
2008-10-29 22:03 14,328 ----a-w c:\windows\potumab.vbs
2008-10-29 22:03 14,029 ----a-w c:\windows\wyfateho.bin
2008-10-29 22:03 12,089 ----a-w c:\windows\xuzog.bat
2008-10-29 22:03 10,714 ----a-w c:\program files\Common Files\setukaz.db
2008-10-28 05:18 19,627 ----a-w c:\documents and settings\All Users\Application Data\egafemedix.vbs
2008-10-28 05:18 19,340 ----a-w c:\program files\Common Files\howyho._sy
2008-10-28 05:18 17,542 ----a-w c:\windows\yromy.bin
2008-10-28 05:18 15,515 ----a-w c:\documents and settings\Sloane\Application Data\mapijunyc.exe
2008-10-28 05:18 14,571 ----a-w c:\windows\ecapeza.reg
2008-10-28 05:18 14,447 ----a-w c:\program files\Common Files\mobe._sy
2008-10-28 05:18 12,638 ----a-w c:\windows\silylovihe.com
2008-10-28 05:18 12,627 ----a-w c:\documents and settings\Sloane\Application Data\zuhyc.reg
2008-10-28 05:18 12,477 ----a-w c:\documents and settings\All Users\Application Data\ybakivymu.sys
2008-10-28 05:18 11,723 ----a-w c:\windows\eremis.bat
2008-10-27 02:01 --------- d-----w c:\program files\SecondLife
2008-10-25 02:02 --------- d-----w c:\documents and settings\Sloane\Application Data\AdobeUM
2008-10-24 11:10 453,632 ----a-w c:\windows\system32\drivers\mrxsmb.sys
2008-10-20 10:20 --------- d-----w c:\documents and settings\Sydney\Application Data\AdobeUM
2008-10-06 21:29 --------- d-----w c:\documents and settings\Sydney\Application Data\LimeWire
2008-09-10 20:33 30,776 -c--a-w c:\documents and settings\Sydney\Application Data\GDIPFONTCACHEV1.DAT
2008-03-07 01:52 30,776 -c--a-w c:\documents and settings\Sloane\Application Data\GDIPFONTCACHEV1.DAT
2007-10-13 14:19 60,968 ----a-w c:\documents and settings\Charles\GoToAssistDownloadHelper.exe
2007-01-06 07:11 1 -c--a-w c:\documents and settings\Sloane\SI.bin
2005-06-17 07:57 774,144 -c--a-w c:\program files\RngInterstitial.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ctfmon.exe"="c:\windows\system32\ctfmon.exe" [2004-08-04 15360]
"swg"="c:\program files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2007-07-12 68856]
"msnmsgr"="c:\program files\MSN Messenger\msnmsgr.exe" [2007-01-19 5674352]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Apoint"="c:\program files\Apoint\Apoint.exe" [2004-09-13 155648]
"UMonit"="c:\windows\system32\umonit.exe" [2004-05-11 53248]
"IntelZeroConfig"="c:\program files\Intel\Wireless\bin\ZCfgSvc.exe" [2006-04-14 667718]
"IntelWireless"="c:\program files\Intel\Wireless\Bin\ifrmewrk.exe" [2006-04-14 602182]
"TkBellExe"="c:\program files\Common Files\Real\Update_OB\realsched.exe" [2005-07-27 180269]
"basicsmssmenu"="c:\program files\Seagate\Basics\Basics Status\MaxMenuMgrBasics.exe" [2007-10-09 169328]
"SunJavaUpdateSched"="c:\program files\Java\jre1.6.0_07\bin\jusched.exe" [2008-06-10 144784]
"QuickTime Task"="c:\program files\QuickTime\QTTask.exe" [2008-09-06 413696]
"iTunesHelper"="c:\program files\iTunes\iTunesHelper.exe" [2008-09-10 289576]
c:\documents and settings\Sloane\Start Menu\Programs\Startup\
GameSpot Download Manager.lnk - c:\program files\GameSpot\GDM_TrayApp.exe [2007-05-09 237568]
LimeWire On Startup.lnk - c:\program files\LimeWire\LimeWire.exe [2008-02-08 147456]
[HKEY_CURRENT_USER\software\microsoft\windows\currentversion\policies\explorer]
"NoViewOnDrive"= 0 (0x0)
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
"UpdatesDisableNotify"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"EnableFirewall"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\Messenger\\msmsgs.exe"=
"c:\\WINDOWS\\pchealth\\helpctr\\binaries\\HelpCtr.exe"=
"c:\\Program Files\\AIM\\aim.exe"=
"c:\\Program Files\\LimeWire\\LimeWire.exe"=
"c:\\Program Files\\Veoh Networks\\Veoh\\VeohClient.exe"=
"c:\\Program Files\\MSN Messenger\\msnmsgr.exe"=
"c:\\Program Files\\MSN Messenger\\livecall.exe"=
"c:\\Program Files\\SecondLife\\SLVoice.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\iTunes\\iTunes.exe"=
R2 DNADownloader;DNADownloader;c:\program files\GameSpot\DownloadManager_Win32.exe [2007-05-09 700416]
S3 cdspacex;cdspacex;c:\windows\system32\DRIVERS\CDSPACEX.sys []
S3 fixustor;fixustor;c:\windows\system32\drivers\fixustor.sys [2005-07-13 6656]
S3 TwoRabts;Two Rabbits Live Bus;c:\windows\system32\DRIVERS\TwoRabts.sys []
S3 w600bus;Sony Ericsson W600 driver (WDM);c:\windows\system32\DRIVERS\w600bus.sys []
S3 w600mdfl;Sony Ericsson W600 USB WMC Modem Filter;c:\windows\system32\DRIVERS\w600mdfl.sys []
S3 w600mdm;Sony Ericsson W600 USB WMC Modem Drivers;c:\windows\system32\DRIVERS\w600mdm.sys []
S3 w600mgmt;Sony Ericsson W600 USB WMC Device Management Drivers;c:\windows\system32\DRIVERS\w600mgmt.sys []
S3 w600obex;Sony Ericsson W600 USB WMC OBEX Interface Drivers;c:\windows\system32\DRIVERS\w600obex.sys []
.
Contents of the 'Scheduled Tasks' folder
2008-11-12 c:\windows\Tasks\AppleSoftwareUpdate.job
- c:\program files\Apple Software Update\SoftwareUpdate.exe [2008-07-30 11:34]
.
**************************************************************************
catchme 0.3.1367 W2K/XP/Vista - rootkit/stealth malware detector by Gmer,
http://www.gmer.netRootkit scan 2008-12-05 23:17:30
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
UMonit = c:\windows\system32\umonit.exe??ed1&Pid_8?????VID808?????Uf?C?USB\RO8???UB?0???????????????????????????w?U??????????tq7?l??????|p??|????m??|C??w?????????Uf?B$?|???w???w*?,??Uf????????????????????????????????w????????????tq7?????T?????7?????tq7???????=????
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(776)
c:\windows\System32\BCMLogon.dll
.
------------------------ Other Running Processes ------------------------
.
c:\program files\Intel\Wireless\Bin\EvtEng.exe
c:\program files\Intel\Wireless\Bin\S24EvMon.exe
c:\program files\Intel\Wireless\Bin\WLKEEPER.exe
c:\windows\system32\WLTRYSVC.EXE
c:\windows\system32\BCMWLTRY.EXE
c:\program files\Lavasoft\Ad-Aware\aawservice.exe
c:\program files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
c:\program files\Seagate\Basics\Service\SyncServicesBasics.exe
c:\program files\Bonjour\mDNSResponder.exe
c:\program files\Cisco Systems\VPN Client\cvpnd.exe
c:\program files\Common Files\Microsoft Shared\VS7Debug\mdm.exe
c:\program files\Dell\NicConfigSvc\NicConfigSvc.exe
c:\windows\system32\nvsvc32.exe
c:\program files\Intel\Wireless\Bin\RegSrvc.exe
c:\windows\system32\wdfmgr.exe
c:\program files\Apoint\ApntEx.exe
c:\program files\iPod\bin\iPodService.exe
c:\program files\Real\RealPlayer\realplay.exe
.
**************************************************************************
.
Completion time: 2008-12-05 23:20:18 - machine was rebooted
ComboFix-quarantined-files.txt 2008-12-06 04:20:11
Pre-Run: 3,264,581,632 bytes free
Post-Run: 4,820,348,928 bytes free
233 --- E O F --- 2008-11-12 01:14:11
***************************
HIJACK LOG
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 11:26:26 PM, on 12/5/2008
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v7.00 (7.00.6000.16735)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Intel\Wireless\Bin\EvtEng.exe
C:\Program Files\Intel\Wireless\Bin\S24EvMon.exe
C:\Program Files\Intel\Wireless\Bin\WLKeeper.exe
C:\WINDOWS\System32\wltrysvc.exe
C:\WINDOWS\System32\bcmwltry.exe
C:\Program Files\Lavasoft\Ad-Aware\aawservice.exe
C:\WINDOWS\system32\spoolsv.exe
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\Program Files\Seagate\Basics\Service\SyncServicesBasics.exe
C:\Program Files\Bonjour\mDNSResponder.exe
C:\Program Files\Cisco Systems\VPN Client\cvpnd.exe
C:\Program Files\GameSpot\DownloadManager_Win32.exe
C:\Program Files\Common Files\Microsoft Shared\VS7Debug\mdm.exe
C:\Program Files\Dell\NICCONFIGSVC\NICCONFIGSVC.exe
C:\WINDOWS\system32\nvsvc32.exe
C:\Program Files\Intel\Wireless\Bin\RegSrvc.exe
C:\WINDOWS\system32\svchost.exe
C:\Program Files\Apoint\Apoint.exe
C:\WINDOWS\system32\umonit.exe
C:\Program Files\Intel\Wireless\bin\ZCfgSvc.exe
C:\Program Files\Intel\Wireless\Bin\ifrmewrk.exe
C:\Program Files\Common Files\Real\Update_OB\realsched.exe
C:\Program Files\Java\jre1.6.0_07\bin\jusched.exe
C:\Program Files\QuickTime\QTTask.exe
C:\Program Files\iTunes\iTunesHelper.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
C:\Program Files\Apoint\Apntex.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\WINDOWS\system32\wuauclt.exe
C:\WINDOWS\explorer.exe
C:\Program Files\Trend Micro\HijackThis\HijackThis.exe
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL =
http://go.microsoft.com/fwlink/?LinkId=69157R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL =
http://go.microsoft.com/fwlink/?LinkId=54896R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page =
http://go.microsoft.com/fwlink/?LinkId=54896R1 - HKCU\Software\Microsoft\Internet Connection Wizard,ShellNext =
http://www.dell4me.com/mywayO3 - Toolbar: &Google - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - c:\program files\google\googletoolbar2.dll
O3 - Toolbar: Veoh Browser Plug-in - {D0943516-5076-4020-A3B5-AEFAF26AB263} - C:\Program Files\Veoh Networks\Veoh\Plugins\reg\VeohToolbar.dll
O4 - HKLM\..\Run: [Apoint] C:\Program Files\Apoint\Apoint.exe
O4 - HKLM\..\Run: [UMonit] C:\WINDOWS\system32\umonit.exe
O4 - HKLM\..\Run: [IntelZeroConfig] "C:\Program Files\Intel\Wireless\bin\ZCfgSvc.exe"
O4 - HKLM\..\Run: [IntelWireless] "C:\Program Files\Intel\Wireless\Bin\ifrmewrk.exe" /tf Intel PROSet/Wireless
O4 - HKLM\..\Run: [TkBellExe] "C:\Program Files\Common Files\Real\Update_OB\realsched.exe" -osboot
O4 - HKLM\..\Run: [basicsmssmenu] "C:\Program Files\Seagate\Basics\Basics Status\MaxMenuMgrBasics.exe"
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Java\jre1.6.0_07\bin\jusched.exe"
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\QTTask.exe" -atboottime
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [swg] C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
O4 - HKCU\..\Run: [msnmsgr] "C:\Program Files\MSN Messenger\msnmsgr.exe" /background
O8 - Extra context menu item: &Search -
http://bar.mywebsearch.com/menusearch.h ... xmk870BYUSO8 - Extra context menu item: E&xport to Microsoft Excel -
res://C:\PROGRA~1\MICROS~4\Office10\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_07\bin\ssv.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_07\bin\ssv.dll
O9 - Extra button: AIM - {AC9E2541-2814-11d5-BC6D-00B0D0A1DE45} - C:\Program Files\AIM\aim.exe
O9 - Extra button: (no name) - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O9 - Extra 'Tools' menuitem: Spybot - Search & Destroy Configuration - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O10 - Unknown file in Winsock LSP: c:\windows\system32\nwprovau.dll
O16 - DPF: {17492023-C23A-453E-A040-C7C580BBF700} (Windows Genuine Advantage Validation Tool) -
http://go.microsoft.com/fwlink/?linkid=39204O16 - DPF: {49232000-16E4-426C-A231-62846947304B} -
http://ipgweb.cce.hp.com/rdqnbk/downloads/sysinfo.cabO16 - DPF: {4ED9DDF0-7479-4BBE-9335-5A1EDB1D8A21} -
http://download.mcafee.com/molbin/share ... insctl.cabO16 - DPF: {8E0D4DE5-3180-4024-A327-4DFAD1796A8D} (MessengerStatsClient Class) -
http://messenger.zone.msn.com/binary/Me ... b31267.cabO16 - DPF: {BCC0FF27-31D9-4614-A68E-C18E1ADA4389} -
http://download.mcafee.com/molbin/share ... cgdmgr.cabO16 - DPF: {C3F79A2B-B9B4-4A66-B012-3EE46475B072} (MessengerStatsClient Class) -
http://messenger.zone.msn.com/binary/Me ... b56907.cabO23 - Service: Lavasoft Ad-Aware Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware\aawservice.exe
O23 - Service: Apple Mobile Device - Apple Inc. - C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
O23 - Service: Basics Service - Seagate Technology LLC - C:\Program Files\Seagate\Basics\Service\SyncServicesBasics.exe
O23 - Service: Bonjour Service - Apple Inc. - C:\Program Files\Bonjour\mDNSResponder.exe
O23 - Service: Cisco Systems, Inc. VPN Service (CVPND) - Cisco Systems, Inc. - C:\Program Files\Cisco Systems\VPN Client\cvpnd.exe
O23 - Service: DNADownloader - CNET Networks - C:\Program Files\GameSpot\DownloadManager_Win32.exe
O23 - Service: Intel(R) PROSet/Wireless Event Log (EvtEng) - Intel Corporation - C:\Program Files\Intel\Wireless\Bin\EvtEng.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: InstallDriver Table Manager (IDriverT) - Macrovision Corporation - C:\Program Files\Common Files\InstallShield\Driver\1150\Intel 32\IDriverT.exe
O23 - Service: iPod Service - Apple Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: NICCONFIGSVC - Dell Inc. - C:\Program Files\Dell\NICCONFIGSVC\NICCONFIGSVC.exe
O23 - Service: NVIDIA Display Driver Service (NVSvc) - NVIDIA Corporation - C:\WINDOWS\system32\nvsvc32.exe
O23 - Service: Intel(R) PROSet/Wireless Registry Service (RegSrvc) - Intel Corporation - C:\Program Files\Intel\Wireless\Bin\RegSrvc.exe
O23 - Service: Intel(R) PROSet/Wireless Service (S24EventMonitor) - Intel Corporation - C:\Program Files\Intel\Wireless\Bin\S24EvMon.exe
O23 - Service: Intel(R) PROSet/Wireless SSO Service (WLANKEEPER) - Intel(R) Corporation - C:\Program Files\Intel\Wireless\Bin\WLKeeper.exe
O23 - Service: Dell Wireless WLAN Tray Service (wltrysvc) - Unknown owner - C:\WINDOWS\System32\wltrysvc.exe
--
End of file - 7321 bytes