Here are the three logs. See note at the end.
ComboFix 08-05-21.3 - john garcia 2008-05-25 8:56:55.7 - NTFSx86
Microsoft Windows XP Home Edition 5.1.2600.2.1252.1.1033.18.1596 [GMT -7:00]
Running from: C:\Documents and Settings\john garcia\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\john garcia\Desktop\CFScript.txt
* Created a new restore point
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
C:\Program Files\Trend Micro
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080524-155923-211
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080524-155923-221
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080524-155923-396
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080524-155923-803
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080524-155923-803.dll
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080525-085253-179
C:\Program Files\Trend Micro\Crusty.exe\backups\backup-20080525-085253-511
C:\Program Files\Trend Micro\Crusty.exe\Crusty.exe.exe
C:\Program Files\Trend Micro\Crusty.exe\hijackthis.log
C:\Program Files\Trend Micro\Crusty.exe\hijackthislog.txt
C:\Program Files\Trend Micro\Crusty.exe\john garcia.exe
.
((((((((((((((((((((((((( Files Created from 2008-04-25 to 2008-05-25 )))))))))))))))))))))))))))))))
.
2008-05-23 10:24 . 2008-05-23 10:24 <DIR> d-------- C:\Deckard
2008-05-20 10:36 . 2008-05-20 10:36 <DIR> d-------- C:\Documents and Settings\Administrator\Application Data\Grisoft
2008-05-18 10:43 . 2008-05-18 10:43 <DIR> d-------- C:\WINDOWS\system32\Dell
2008-05-17 19:59 . 2008-05-17 19:59 206 --a------ C:\WINDOWS\system32\MRT.INI
2008-05-17 16:42 . 2008-05-17 16:42 <DIR> d-------- C:\Documents and Settings\john garcia\Application Data\Malwarebytes
2008-05-17 16:42 . 2008-05-17 16:42 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Malwarebytes
2008-05-17 16:29 . 2007-09-06 00:22 289,144 --a------ C:\WINDOWS\system32\VCCLSID.exe
2008-05-17 16:29 . 2006-04-27 17:49 288,417 --a------ C:\WINDOWS\system32\SrchSTS.exe
2008-05-17 16:29 . 2008-05-15 23:22 86,528 --a------ C:\WINDOWS\system32\VACFix.exe
2008-05-17 16:29 . 2008-04-28 08:03 82,944 --a------ C:\WINDOWS\system32\IEDFix.exe
2008-05-17 16:29 . 2008-04-28 08:03 82,944 --a------ C:\WINDOWS\system32\404Fix.exe
2008-05-17 16:29 . 2003-06-05 21:13 53,248 --a------ C:\WINDOWS\system32\Process.exe
2008-05-17 16:29 . 2004-07-31 18:50 51,200 --a------ C:\WINDOWS\system32\dumphive.exe
2008-05-17 16:29 . 2007-10-04 00:36 25,600 --a------ C:\WINDOWS\system32\WS2Fix.exe
2008-05-17 14:09 . 2008-05-17 14:09 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\SUPERAntiSpyware.com
2008-05-17 14:08 . 2008-05-22 12:23 <DIR> d-------- C:\Documents and Settings\john garcia\Application Data\SUPERAntiSpyware.com
2008-05-16 21:17 . 2008-05-17 01:19 <DIR> d-------- C:\Documents and Settings\john garcia\.housecall6.6
2008-05-16 21:12 . 2008-05-24 15:57 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Google Updater
2008-05-15 11:40 . 2008-05-15 11:40 <DIR> d-------- C:\Documents and Settings\john garcia\Application Data\TmpRecentIcons
2008-05-11 03:58 . 2008-05-11 03:58 <DIR> d-------- C:\Documents and Settings\john garcia\Application Data\Lexmark Productivity Studio
2008-05-10 16:22 . 2008-05-10 16:22 <DIR> d-------- C:\Documents and Settings\john garcia\Application Data\FaxCtr
2008-05-10 16:02 . 2008-05-10 16:04 <DIR> d-------- C:\Documents and Settings\All Users\Lx_cats
2008-05-10 16:00 . 2007-02-22 00:13 45,056 --a------ C:\WINDOWS\system32\LXF3PMON.DLL
2008-05-10 16:00 . 2007-02-22 00:12 32,768 --a------ C:\WINDOWS\system32\LXF3FXPU.DLL
2008-05-10 15:59 . 2008-05-10 16:00 <DIR> d-------- C:\Program Files\Lexmark Fax Solutions
2008-05-10 15:59 . 2008-05-10 15:59 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\FaxCtr
2008-05-10 15:59 . 2006-05-31 12:51 339,968 --a------ C:\WINDOWS\system32\IMGMAN32.DLL
2008-05-10 15:59 . 2006-05-31 12:51 98,345 --a------ C:\WINDOWS\system32\IMHOST32.DLL
2008-05-10 15:59 . 2006-05-31 12:51 98,304 --a------ C:\WINDOWS\system32\IM31XPNG.DEL
2008-05-10 15:59 . 2006-05-31 12:51 69,632 --a------ C:\WINDOWS\system32\IM31XTIF.DEL
2008-05-10 15:59 . 2006-05-31 12:51 49,152 --a------ C:\WINDOWS\system32\IM31IMG.DIL
2008-05-10 15:59 . 2006-11-07 08:02 36,864 --a------ C:\WINDOWS\system32\lxf3oem.dll
2008-05-10 15:59 . 2007-02-22 00:15 12,288 --a------ C:\WINDOWS\system32\LXF3PMRC.DLL
2008-05-10 15:56 . 2007-02-19 13:00 1,645,320 --a------ C:\WINDOWS\system32\gdiplus.dll
2008-05-10 15:48 . 2008-05-10 16:01 <DIR> d-------- C:\Program Files\Lexmark 3500-4500 Series
2008-05-10 15:48 . 2007-05-17 08:00 311,296 --a------ C:\WINDOWS\system32\lxdihcp.dll
2008-05-10 15:48 . 2007-05-17 07:59 294,912 --a------ C:\WINDOWS\system32\lxdiinst.dll
2008-05-10 15:48 . 2007-01-22 02:53 60 --ah----- C:\WINDOWS\system32\lxdirwrd.ini
2008-05-10 15:46 . 2008-05-10 15:46 <DIR> d-------- C:\logs
2008-05-10 15:46 . 2007-03-30 07:13 344,064 -ra------ C:\WINDOWS\system32\lxdicoin.dll
2008-05-10 15:46 . 2007-06-11 07:01 1,900 -ra------ C:\WINDOWS\system32\lxdi.loc
2008-05-06 16:18 . 2008-05-06 16:19 <DIR> d-------- C:\Program Files\505 Game Collection
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-05-24 23:06 --------- d-----w C:\Program Files\Google
2008-05-24 23:05 --------- d-----w C:\Program Files\Spybot - Search & Destroy
2008-05-24 23:05 --------- d-----w C:\Program Files\QuickTime
2008-05-24 23:05 --------- d-----w C:\Program Files\Microsoft IntelliType Pro
2008-05-24 23:05 --------- d-----w C:\Program Files\Microsoft IntelliPoint
2008-05-24 23:05 --------- d-----w C:\Program Files\DellSupport
2008-05-24 23:05 --------- d-----w C:\Program Files\Dell Photo AIO Printer 924
2008-05-22 19:23 --------- d-----w C:\Program Files\Common Files\Wise Installation Wizard
2008-05-20 05:01 --------- d-----w C:\Documents and Settings\john garcia\Application Data\AVG7
2008-05-20 00:12 --------- d-----w C:\Program Files\Dl_cats
2008-05-18 17:53 --------- d-----w C:\Documents and Settings\john garcia\Application Data\Yahoo!
2008-05-18 17:43 --------- d-----w C:\Program Files\Dell
2008-05-17 03:54 --------- d-----w C:\Program Files\Java
2008-05-10 22:58 --------- d-----w C:\Program Files\Abbyy FineReader 6.0 Sprint
2008-05-06 23:25 --------- d--h--w C:\Program Files\InstallShield Installation Information
2008-03-27 08:12 151,583 ----a-w C:\WINDOWS\system32\msjint40.dll
2008-03-27 08:12 151,583 ------w C:\WINDOWS\system32\dllcache\msjint40.dll
2008-03-19 09:47 1,845,248 ----a-w C:\WINDOWS\system32\win32k.sys
2008-03-19 09:47 1,845,248 ------w C:\WINDOWS\system32\dllcache\win32k.sys
2008-03-02 01:36 3,591,680 ------w C:\WINDOWS\system32\dllcache\mshtml.dll
2008-02-29 08:55 70,656 ------w C:\WINDOWS\system32\dllcache\ie4uinit.exe
2008-02-29 08:55 625,664 ----a-w C:\WINDOWS\system32\dllcache\iexplore.exe
2008-02-25 21:53 15,360 ----a-w C:\WINDOWS\system32\dllcache\ctfmon.exe
2008-02-25 21:53 15,360 ----a-w C:\WINDOWS\system32\ctfmon.exe
2006-09-24 16:52 774,144 ----a-w C:\Program Files\RngInterstitial.dll
2008-02-23 10:53 56 --sh--r C:\WINDOWS\system32\70EF0442AF.sys
2008-02-23 10:53 4,236 -csha-w C:\WINDOWS\system32\KGyGaAvL.sys
.
((((((((((((((((((((((((((((( snapshot_2008-05-24_16.16.10.60 )))))))))))))))))))))))))))))))))))))))))
.
- 2008-05-24 23:09:14 2,048 --s-a-w C:\WINDOWS\bootstat.dat
+ 2008-05-25 15:49:55 2,048 --s-a-w C:\WINDOWS\bootstat.dat
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ctfmon.exe"="C:\WINDOWS\system32\ctfmon.exe" [2008-02-25 14:53 15360]
"DellSupport"="C:\Program Files\DellSupport\DSAgnt.exe" [2008-02-26 17:24 460784]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"YSearchProtection"="C:\Program Files\Yahoo!\Search Protection\SearchProtection.exe" [2008-02-26 17:24 224248]
"SunJavaUpdateSched"="C:\Program Files\Java\jre1.6.0_05\bin\jusched.exe" [2008-02-22 04:25 144784]
"SoundMAXPnP"="C:\Program Files\Analog Devices\Core\smax4pnp.exe" [2008-02-04 13:39 1404928]
"RealTray"="C:\Program Files\Real\RealPlayer\RealPlay.exe" [2008-02-04 13:39 26112]
"MimBoot"="C:\PROGRA~1\MUSICM~1\MUSICM~3\mimboot.exe" [2008-02-04 13:39 8192]
"lxdimon.exe"="C:\Program Files\Lexmark 3500-4500 Series\lxdimon.exe" [2007-07-16 09:54 434864]
"lxdiamon"="C:\Program Files\Lexmark 3500-4500 Series\lxdiamon.exe" [2007-07-16 09:54 25264]
"itype"="C:\Program Files\Microsoft IntelliType Pro\itype.exe" [2008-02-04 13:40 576320]
"ISUSScheduler"="C:\Program Files\Common Files\InstallShield\UpdateService\issch.exe" [2008-02-04 13:39 81920]
"ISUSPM Startup"="c:\Program Files\Common Files\InstallShield\UpdateService\isuspm.exe" [2008-02-04 11:20 249856]
"IntelliPoint"="C:\Program Files\Microsoft IntelliPoint\ipoint.exe" [2008-02-04 13:40 600896]
"igfxtray"="C:\WINDOWS\system32\igfxtray.exe" [2008-02-04 13:39 94208]
"igfxpers"="C:\WINDOWS\system32\igfxpers.exe" [2008-02-04 13:39 114688]
"igfxhkcmd"="C:\WINDOWS\system32\hkcmd.exe" [2008-02-04 13:39 77824]
"FaxCenterServer"="C:\Program Files\\Lexmark Fax Solutions\fm3032.exe" [2007-07-16 09:54 311984]
"DMXLauncher"="C:\Program Files\Dell\Media Experience\DMXLauncher.exe" [2008-02-04 13:39 86016]
"dlccmon.exe"="C:\Program Files\Dell Photo AIO Printer 924\dlccmon.exe" [2008-02-04 13:39 425984]
"DLCCCATS"="C:\WINDOWS\System32\spool\DRIVERS\W32X86\3\DLCCtime.dll" [2005-06-07 05:38 69632]
"Corel Photo Downloader"="C:\Program Files\Corel\Corel Photo Album 6\MediaDetect.exe" [2008-02-04 13:40 106496]
"AVG7_CC"="C:\PROGRA~1\Grisoft\AVG7\avgcc.exe" [2008-04-17 09:29 579584]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"AVG7_Run"="C:\PROGRA~1\Grisoft\AVG7\avgw.exe" [2008-02-27 18:07 219136]
C:\Documents and Settings\All Users\Start Menu\Programs\Startup\
Digital Line Detect.lnk - C:\Program Files\Digital Line Detect\DLG.exe [2005-12-19 19:44:06 24576]
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"EnableFirewall"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"C:\\Program Files\\Yahoo!\\Messenger\\YServer.exe"=
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"C:\\Program Files\\Grisoft\\AVG7\\avginet.exe"=
"C:\\Program Files\\Grisoft\\AVG7\\avgamsvr.exe"=
"C:\\Program Files\\Grisoft\\AVG7\\avgcc.exe"=
"C:\\Program Files\\Grisoft\\AVG7\\avgemc.exe"=
"C:\\WINDOWS\\system32\\lxdicoms.exe"=
"C:\\Program Files\\Lexmark 3500-4500 Series\\lxdiamon.exe"=
"C:\\Program Files\\Lexmark 3500-4500 Series\\App4R.exe"=
"C:\\Program Files\\Abbyy FineReader 6.0 Sprint\\Scan\\ScanMan6.exe"=
"C:\\Program Files\\Lexmark Fax Solutions\\FaxCtr.exe"=
"C:\\Program Files\\Lexmark 3500-4500 Series\\lxdimon.exe"=
"C:\\WINDOWS\\system32\\spool\\drivers\\w32x86\\3\\lxdipswx.exe"=
"C:\\WINDOWS\\system32\\spool\\drivers\\w32x86\\3\\lxditime.exe"=
"C:\\WINDOWS\\system32\\spool\\drivers\\w32x86\\3\\lxdijswx.exe"=
R2 lxdi_device;lxdi_device;C:\WINDOWS\system32\lxdicoms.exe [2007-06-11 07:14]
R2 lxdiCATSCustConnectService;lxdiCATSCustConnectService;C:\WINDOWS\System32\spool\DRIVERS\W32X86\3\\lxdiserv.exe [2007-06-11 07:14]
*Newly Created Service* - CATCHME
.
**************************************************************************
catchme 0.3.1361 W2K/XP/Vista - rootkit/stealth malware detector by Gmer,
http://www.gmer.netRootkit scan 2008-05-25 08:59:16
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
Completion time: 2008-05-25 9:02:02
ComboFix-quarantined-files.txt 2008-05-25 16:01:26
ComboFix2.txt 2008-05-24 23:17:09
ComboFix3.txt 2008-05-22 20:17:51
ComboFix4.txt 2008-05-18 02:09:11
Pre-Run: 64,370,495,488 bytes free
Post-Run: 64,354,295,808 bytes free
179 --- E O F --- 2008-05-25 00:05:49
Malwarebytes' Anti-Malware 1.12
Database version: 785
Scan type: Full Scan (C:\|)
Objects scanned: 89351
Time elapsed: 17 minute(s), 37 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 2
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\QooBox\Quarantine\C\WINDOWS\system32\drivers\nsX73.sys.vir (Trojan.Agent) -> Quarantined and deleted successfully.
C:\System Volume Information\_restore{202550A8-7A33-4BCA-9586-051D24DDBF8F}\RP915\A0093106.sys (Trojan.Agent) -> Quarantined and deleted successfully.
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 10:11:56 AM, on 5/25/2008
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v7.00 (7.00.6000.16640)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\WINDOWS\system32\spoolsv.exe
C:\PROGRA~1\Grisoft\AVG7\avgamsvr.exe
C:\PROGRA~1\Grisoft\AVG7\avgupsvc.exe
C:\PROGRA~1\Grisoft\AVG7\avgemc.exe
C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
C:\WINDOWS\System32\spool\DRIVERS\W32X86\3\lxdiserv.exe
C:\WINDOWS\system32\lxdicoms.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\Explorer.EXE
C:\WINDOWS\system32\wscntfy.exe
C:\Program Files\Yahoo!\Search Protection\SearchProtection.exe
C:\Program Files\Analog Devices\Core\smax4pnp.exe
C:\Program Files\Real\RealPlayer\RealPlay.exe
C:\Program Files\Lexmark 3500-4500 Series\lxdimon.exe
C:\Program Files\Lexmark 3500-4500 Series\lxdiamon.exe
C:\Program Files\Microsoft IntelliType Pro\itype.exe
C:\Program Files\Common Files\InstallShield\UpdateService\issch.exe
C:\Program Files\Microsoft IntelliPoint\ipoint.exe
C:\PROGRA~1\MUSICM~1\MUSICM~3\MMDiag.exe
C:\WINDOWS\system32\igfxpers.exe
C:\WINDOWS\system32\hkcmd.exe
C:\Program Files\Dell\Media Experience\DMXLauncher.exe
C:\Program Files\Dell Photo AIO Printer 924\dlccmon.exe
C:\Program Files\Corel\Corel Photo Album 6\MediaDetect.exe
C:\PROGRA~1\Grisoft\AVG7\avgcc.exe
C:\Program Files\Java\jre1.6.0_06\bin\jusched.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\DellSupport\DSAgnt.exe
C:\Program Files\Digital Line Detect\DLG.exe
C:\Program Files\MUSICMATCH\Musicmatch Jukebox\mim.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\system32\dlcccoms.exe
C:\WINDOWS\system32\wuauclt.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\Documents and Settings\john garcia\Desktop\HiJackThis.exe
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Start Page =
http://yahoo.com/R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL =
http://go.microsoft.com/fwlink/?LinkId=69157R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL =
http://go.microsoft.com/fwlink/?LinkId=54896R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page =
http://go.microsoft.com/fwlink/?LinkId=54896O2 - BHO: Spybot-S&D IE Protection - {53707962-6F74-2D53-2644-206D7942484F} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O2 - BHO: Yahoo! IE Services Button - {5BAB4B5B-68BC-4B02-94D6-2FC0DE4A7897} - C:\Program Files\Yahoo!\Common\yiesrvc.dll
O2 - BHO: SSVHelper Class - {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O4 - HKLM\..\Run: [YSearchProtection] "C:\Program Files\Yahoo!\Search Protection\SearchProtection.exe"
O4 - HKLM\..\Run: [SoundMAXPnP] "C:\Program Files\Analog Devices\Core\smax4pnp.exe"
O4 - HKLM\..\Run: [RealTray] "C:\Program Files\Real\RealPlayer\RealPlay.exe" SYSTEMBOOTHIDEPLAYER
O4 - HKLM\..\Run: [MimBoot] C:\PROGRA~1\MUSICM~1\MUSICM~3\mimboot.exe
O4 - HKLM\..\Run: [lxdimon.exe] "C:\Program Files\Lexmark 3500-4500 Series\lxdimon.exe"
O4 - HKLM\..\Run: [lxdiamon] "C:\Program Files\Lexmark 3500-4500 Series\lxdiamon.exe"
O4 - HKLM\..\Run: [itype] "C:\Program Files\Microsoft IntelliType Pro\itype.exe"
O4 - HKLM\..\Run: [ISUSScheduler] "C:\Program Files\Common Files\InstallShield\UpdateService\issch.exe" -start
O4 - HKLM\..\Run: [ISUSPM Startup] "C:\Program Files\Common Files\InstallShield\UpdateService\isuspm.exe" -startup
O4 - HKLM\..\Run: [IntelliPoint] "C:\Program Files\Microsoft IntelliPoint\ipoint.exe"
O4 - HKLM\..\Run: [igfxtray] C:\WINDOWS\system32\igfxtray.exe
O4 - HKLM\..\Run: [igfxpers] C:\WINDOWS\system32\igfxpers.exe
O4 - HKLM\..\Run: [igfxhkcmd] C:\WINDOWS\system32\hkcmd.exe
O4 - HKLM\..\Run: [FaxCenterServer] "C:\Program Files\\Lexmark Fax Solutions\fm3032.exe" /s
O4 - HKLM\..\Run: [DMXLauncher] "C:\Program Files\Dell\Media Experience\DMXLauncher.exe"
O4 - HKLM\..\Run: [dlccmon.exe] "C:\Program Files\Dell Photo AIO Printer 924\dlccmon.exe"
O4 - HKLM\..\Run: [DLCCCATS] rundll32 C:\WINDOWS\System32\spool\DRIVERS\W32X86\3\DLCCtime.dll,_RunDLLEntry@16
O4 - HKLM\..\Run: [Corel Photo Downloader] C:\Program Files\Corel\Corel Photo Album 6\MediaDetect.exe
O4 - HKLM\..\Run: [AVG7_CC] C:\PROGRA~1\Grisoft\AVG7\avgcc.exe /STARTUP
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Java\jre1.6.0_06\bin\jusched.exe"
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [DellSupport] "C:\Program Files\DellSupport\DSAgnt.exe" /startup
O4 - HKUS\S-1-5-19\..\Run: [AVG7_Run] C:\PROGRA~1\Grisoft\AVG7\avgw.exe /RUNONCE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-20\..\Run: [AVG7_Run] C:\PROGRA~1\Grisoft\AVG7\avgw.exe /RUNONCE (User 'NETWORK SERVICE')
O4 - HKUS\S-1-5-18\..\Run: [AVG7_Run] C:\PROGRA~1\Grisoft\AVG7\avgw.exe /RUNONCE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [AVG7_Run] C:\PROGRA~1\Grisoft\AVG7\avgw.exe /RUNONCE (User 'Default user')
O4 - Global Startup: Digital Line Detect.lnk = ?
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O9 - Extra button: Spyware Doctor - {2D663D1A-8670-49D9-A1A5-4C56B4E14E84} - C:\WINDOWS\system32\shdocvw.dll
O9 - Extra button: Yahoo! Services - {5BAB4B5B-68BC-4B02-94D6-2FC0DE4A7897} - C:\Program Files\Yahoo!\Common\yiesrvc.dll
O9 - Extra button: Real.com - {CD67F990-D8E9-11d2-98FE-00C0F0318AFE} - C:\WINDOWS\system32\shdocvw.dll
O9 - Extra button: (no name) - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O9 - Extra 'Tools' menuitem: Spybot - Search & Destroy Configuration - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O9 - Extra button: (no name) - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra 'Tools' menuitem: @xpsp3res.dll,-20001 - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O16 - DPF: {01A88BB1-1174-41EC-ACCB-963509EAE56B} (SysProWmi Class) -
http://support.dell.com/systemprofiler/SysPro.CABO23 - Service: Ad-Aware 2007 Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
O23 - Service: AVG7 Alert Manager Server (Avg7Alrt) - GRISOFT, s.r.o. - C:\PROGRA~1\Grisoft\AVG7\avgamsvr.exe
O23 - Service: AVG7 Update Service (Avg7UpdSvc) - GRISOFT, s.r.o. - C:\PROGRA~1\Grisoft\AVG7\avgupsvc.exe
O23 - Service: AVG E-mail Scanner (AVGEMS) - GRISOFT, s.r.o. - C:\PROGRA~1\Grisoft\AVG7\avgemc.exe
O23 - Service: dlcc_device - Unknown owner - C:\WINDOWS\system32\dlcccoms.exe
O23 - Service: DSBrokerService - Unknown owner - C:\Program Files\DellSupport\brkrsvc.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: lxdiCATSCustConnectService - Lexmark International, Inc. - C:\WINDOWS\System32\spool\DRIVERS\W32X86\3\\lxdiserv.exe
O23 - Service: lxdi_device - - C:\WINDOWS\system32\lxdicoms.exe
O23 - Service: Intel NCS NetService (NetSvc) - Intel(R) Corporation - C:\Program Files\Intel\PROSetWired\NCS\Sync\NetSvc.exe
O24 - Desktop Component 0: Privacy Protection - (no file)
--
End of file - 7612 bytes
The 024 Desktop Component keeps coming back. I'm positive I checked it both times.
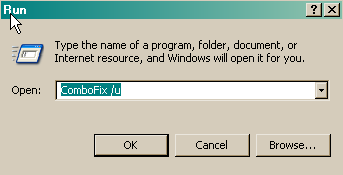
When I tried to open the old HJT icon on my desktop it said:
C:\Qoobox\Quarantine\C\Program Files\Trend Micro\Crusty.exe. And it asked what program I wanted to open it with. So I downloaded a new HJT and ran the scan.